Bpf Filter Cheat Sheet - Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Bpf supports filtering packets, allowing a userspace process to supply a filter program that specifies which packets it wants to receive. Instantly share code, notes, and snippets. They filter on specific flags. The filters below are tcp specific. Primitives usually consist of an id (name or. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. This makes the following filters very useful to capture only the start of traffic,. Use bpf filtering to quickly reduce large packet captures.
Bpf supports filtering packets, allowing a userspace process to supply a filter program that specifies which packets it wants to receive. Primitives usually consist of an id (name or. This makes the following filters very useful to capture only the start of traffic,. The filters below are tcp specific. Use bpf filtering to quickly reduce large packet captures. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. They filter on specific flags. Instantly share code, notes, and snippets.
Bpf supports filtering packets, allowing a userspace process to supply a filter program that specifies which packets it wants to receive. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Primitives usually consist of an id (name or. They filter on specific flags. Use bpf filtering to quickly reduce large packet captures. Instantly share code, notes, and snippets. The filters below are tcp specific. This makes the following filters very useful to capture only the start of traffic,.
featuredimagebpf.jpg
Use bpf filtering to quickly reduce large packet captures. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. Instantly share code, notes, and snippets. Primitives usually consist of an id (name or. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis.
BPF resources FortiNDR Cloud 2023.2.0
The filters below are tcp specific. Bpf supports filtering packets, allowing a userspace process to supply a filter program that specifies which packets it wants to receive. Instantly share code, notes, and snippets. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. Primitives usually consist of an id (name or.
coaxial cavity bpf filter ,five notched filter,ripple filter,4 pole
Primitives usually consist of an id (name or. The filters below are tcp specific. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. Instantly share code, notes, and snippets. They filter on specific flags.
GitHub mikeroyal/eBPFGuide eBPF (extended Berkeley Packet Filter
Bpf supports filtering packets, allowing a userspace process to supply a filter program that specifies which packets it wants to receive. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. This makes the following filters very useful to capture only the start of traffic,. Use bpf filtering to quickly reduce large packet captures. Berkeley packet filter (bpf).
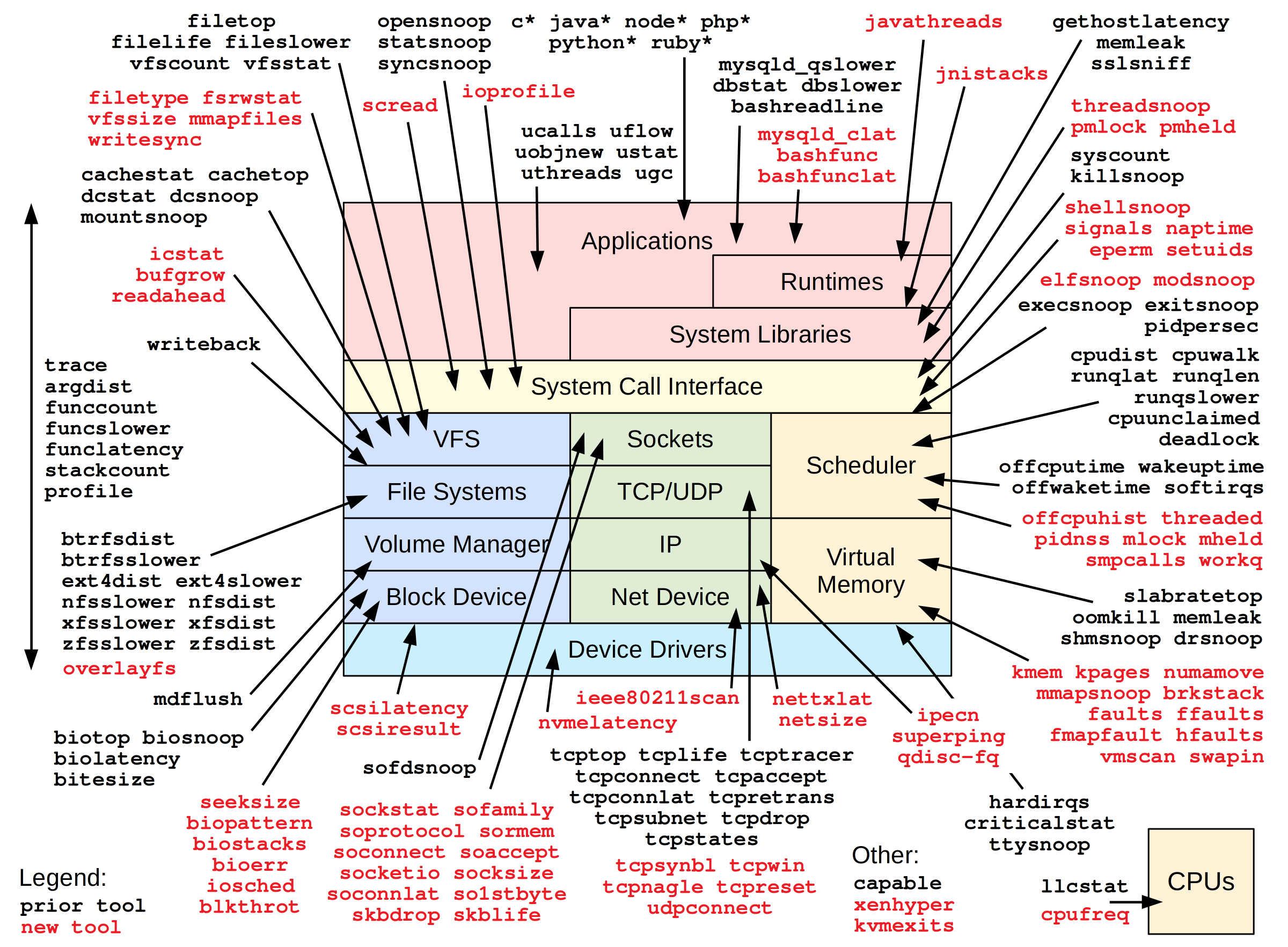
Offensive BPF What's in the bpfcctools box? · Embrace The Red
Primitives usually consist of an id (name or. This makes the following filters very useful to capture only the start of traffic,. The filters below are tcp specific. Instantly share code, notes, and snippets. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives.
GitHub sbabicz/tcpdumpbpfcheatsheet Graphical model of a TCP/IP
They filter on specific flags. Use bpf filtering to quickly reduce large packet captures. The filters below are tcp specific. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis.
BPF cheat sheet
Primitives usually consist of an id (name or. This makes the following filters very useful to capture only the start of traffic,. Instantly share code, notes, and snippets. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis.
bpf693 of 3 Telegraph
This makes the following filters very useful to capture only the start of traffic,. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. Instantly share code, notes, and snippets. They filter on specific flags. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis.
GitHub mikeroyal/eBPFGuide eBPF (extended Berkeley Packet Filter
They filter on specific flags. This makes the following filters very useful to capture only the start of traffic,. Instantly share code, notes, and snippets. Use bpf filtering to quickly reduce large packet captures. Bpf supports filtering packets, allowing a userspace process to supply a filter program that specifies which packets it wants to receive.
Introduction to BPF LINUX Berkeley Packet Filter
Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis. The filters below are tcp specific. Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. They filter on specific flags. Instantly share code, notes, and snippets.
Primitives Usually Consist Of An Id (Name Or.
Use bpf filtering to quickly reduce large packet captures. Instantly share code, notes, and snippets. They filter on specific flags. Berkeley packet filters (bpf) provide a powerful tool for intrusion detection analysis.
Bpf Supports Filtering Packets, Allowing A Userspace Process To Supply A Filter Program That Specifies Which Packets It Wants To Receive.
Berkeley packet filter (bpf) syntax the expression consists of one or more primitives. This makes the following filters very useful to capture only the start of traffic,. The filters below are tcp specific.